With the progress of technology, our daily lives increasingly rely on digital solutions. The internet, smartphones, emails, and cloud computing have become integral parts of our lives, providing convenience, efficiency, and global connectivity. Unfortunately, along with the benefits of digitization, new and increasingly sophisticated threats to online security emerge.
Cybercriminals constantly refine their techniques, leveraging the latest tools and strategies to achieve their objectives. As a result, cybersecurity has become one of the most critical challenges of our time, affecting individuals, businesses, and institutions worldwide. Whether we are regular users or entrepreneurs, we are all susceptible to cyberattacks.
It is essential to recognize that cyber threats know no boundaries. Companies store sensitive customer data and conduct financial transactions, while public institutions gather information about citizens. This makes them valuable targets for cybercriminals who may exploit stolen data in various ways, including identity theft, extortion, or manipulation to gain financial benefits.
Let’s focus on some of the most popular cybersecurity threats.
Phishing
Phishing is a fraudulent technique in which cybercriminals impersonate trusted institutions or individuals by sending email messages, SMS texts, or operating fake websites. The goal is to obtain confidential data, such as passwords, credit card numbers, or personal information. It’s important to pay attention to email addresses, links, and requests for sensitive information.
Malware
Malware is a general term encompassing viruses, trojans, ransomware, and other malicious software. They are designed to damage, steal data, or spy on users. Installing antivirus software, regularly updating systems, and exercising caution when downloading files can help minimize the risk associated with malware.
DDoS Attacks
Distributed Denial of Service (DDoS) attacks involve overwhelming a server or network infrastructure to deny users access to services. These attacks utilize botnets and an excessive number of requests, leading to overload and unavailability of online services. Companies and organizations should invest in proper network protection to minimize the risk of DDoS attacks.
Hacking and Intrusions
Hackers attempt to gain unauthorized access to computer systems and networks. Intrusions can lead to data theft, information manipulation, or data destruction. Strong passwords, two-factor authentication, and monitoring network activity can help secure against hacking attempts.
Social Engineering
Threats associated with social engineering use psychological manipulation to persuade people to take actions that may harm data security. This can include impersonating company employees to obtain confidential information or convincing them to perform undesirable actions. Employee education and awareness of such threats are crucial in combating social engineering.
Application Security Vulnerabilities
Imperfections and security loopholes in software can enable cybercriminals to gain unauthorized access to systems. Companies should regularly test their applications for security and follow best programming practices to minimize the risk of attacks from these types of threats.
Risk and Consequences of Cyber Attacks
Regardless of whether we are regular users, entrepreneurs, or representatives of institutions, everyone is exposed to cybercrime threats that can have a significant impact on our privacy, finances, and reputation. Therefore, awareness, appropriate safeguards, and regular training in cybersecurity are essential to minimize the risks and consequences of attacks in the digital world. Online security should be a priority for anyone who uses the internet and digital technologies.
How to Counter These Threats?
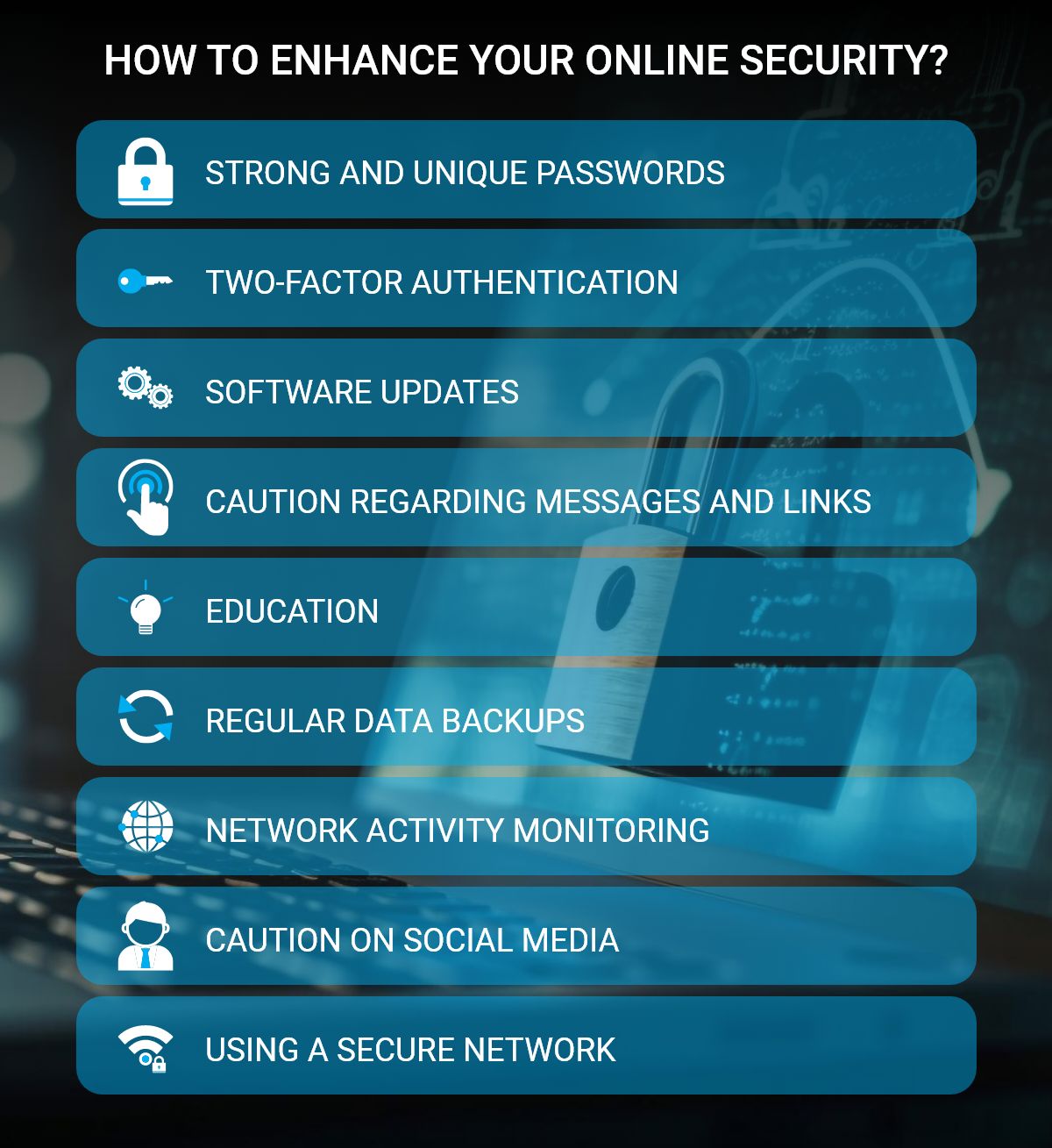
Both individual users and companies or institutions should take appropriate steps to protect their data and minimize the risk of cyber attacks. Here are some key actions that can be taken to enhance online security:
• Avoid using easily guessable passwords. It is recommended to use long, complex, and unique passwords for different accounts. Password managers can also be used to help remember and generate secure passwords.
• Enable two-factor authentication wherever possible to provide an additional layer of protection. It requires providing an additional code or using authentication apps in addition to the password.
• Regularly update operating systems, antivirus software, web browsers, and applications. Updates often include security patches that help minimize vulnerabilities.
• Avoid clicking on suspicious links in emails, SMS messages, or websites. Each suspicious message should be verified directly with the sender.
• For businesses and organizations, cybersecurity education for employees is crucial. Everyone should be aware of the latest threats and know how to defend against them.
• Store sensitive data securely, with encryption being the best method, especially on mobile devices.
• Regularly back up data and store it on independent media or in the cloud. Having a data backup can be helpful in case of a ransomware attack, allowing for easy recovery.
• For businesses and organizations, monitoring network traffic to detect abnormalities and suspicious activities is important.
• Configure privacy settings on social media appropriately to limit access to personal data.
• Avoid using unsecured Wi-Fi networks, especially in public places, where data is most vulnerable to risks.
Let’s remember that cybersecurity is an ongoing process. Threats constantly evolve, so it’s essential to remain vigilant, update our knowledge about security, and adopt the latest technologies and practices to effectively counter cyber attacks. By taking care of our online security, we protect our data, privacy, and avoid potential consequences associated with online attacks.
Cybersecurity is a collective effort that requires continuous attention and education. For individuals and organizations that handle sensitive data, protection against these threats is crucial. Increasing awareness, understanding modern risks, and implementing appropriate technological solutions will help maintain security and peace of mind in today’s digital world.
Remember that cybersecurity is everyone’s concern. Regular software updates, strong passwords, using reliable sources, exercising caution in online communication, and cybersecurity education are key elements in ensuring protection against contemporary threats. Only through conscious and responsible actions can we make our experience in the digital world safer and more rewarding.





